Last week saw me attend the TEISS European Information Security summit down in London. This is one of my annual journeys outside of the education bubble to look at cyber security, resilience and health in the broader industry and enterprise context. I feel it is always important to try and seek diversity and to seek to avoid falling into the issues associated with existing purely within a silo, so stepping outside of my day to day on a regularish basis is a must.
More of the same, but greater volumes and speed.

If I was to summarise one of my main takeaways from the event, it would be that a lot of what I had heard was similar to what I had heard a year before. Cybercrime continues to grow in terms of both threat and in terms of its potential impact. The specific threats, such as ransomware, or social engineering, haven’t really changed but the frequency and speed of attacks has increased. One particular slide looked at national state actors showing how some countries were now down to a breakout time, from compromise to exfiltration, of under 6 minutes. Now it isn’t likely that schools will need to face nation state actors, albeit we could end up as collateral damage, however this increase in speed for nation state actors is likely mirrored for other threat actors, including those schools may actually face. Related to this, one presenter showed screenshots of AI powered cybercrime tools which are now available, highlighting that AI, and in particular Large Language Models, not only have the potential to increase the productivity and efficiency of users, they also have the potential to increase the productivity and efficiency of criminals. I was aware of FraudGPT and WormGPT so this wasn’t new to me however the subsequent slide provided showed an automation and orchestration platform which criminals could use. The combination of AI powered creation tools alongside automation tools gives me concern as it would clearly give the criminals the ability to broadly launch convincing attacks but where any compromise can be quickly leveraged before defenders have an opportunity to react. Think PowerAutomate for criminals. Lots more, better phishing emails, where user errors are quickly capitalised on to deliver malware, extract data or propagate further attacks.
Geo-political instability
Discussion of the impact of geo-political instability and its impact on information security was very interesting especially in considering the room full of cyber security professionals charged with protecting companies and data, including companies responsible for critical national infrastructure. From a school point of view, this might seem to be outside of our wheelhouse however on reflection I wonder about our need to educate students in relation to this. We have already seen that modern warfare now involves a cyber element, with the cyber element often preceding any physical engagement. Do students need to be aware of the implications of globally connected digital services in a world of increasing conflict along national and geographic borders? How might these issues directly impact us, but also what about where we are indirectly impacted or where the impact is subtle manipulation via social media. I suspect there is a whole post possible on this alone.
User awareness and training
I spent a significant part of the conference watching sessions within the Culture and Education stream. There was some good discussion in relation to culture and testing of cyber resilience, particularly the use of phishing awareness testing. These tests are very good at giving us a snapshot or even a longitudinal view as to our general cyber resilience, however they aren’t as useful at an individual user level. To present a staff member or student with some additional training material to undertake following them falling for a phishing test, doesn’t find them are their best in terms of their potential to learn. One presenter presented an alternative view suggesting that all users mean to do the right thing, so therefore we should be asking what it is that makes them do the wrong thing, rather than focusing on how we change individuals behaviour. For me this very often comes down to being time poor and therefore being in a rush or suffering workload issues so I am not sure quite what we can do about this. In my view, the world and our roles only see us adding more tasks and activities, and very seldom do we take things away, therefore it is no wonder that we are time poor and therefore no wonder that in our hurry we fall for social engineering and for phishing emails. That said, it is definitely worth the conversation as to what the barriers to good cyber behaviours are and then looking to see if there is any way to address them. I suspect we wont solve the issue, but I bet there will be some possible quick wins.
Recovery over prevention
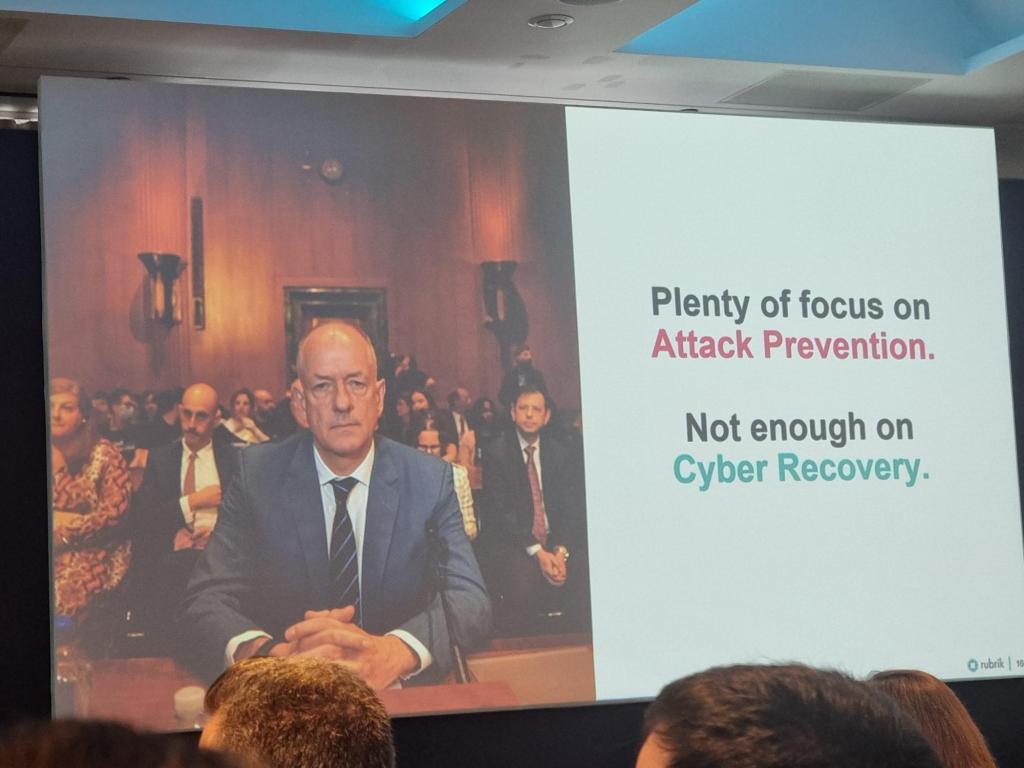
One presenter made a very interesting observation that we continue to spend too much time focussed on prevention over spending time looking at how we might respond and recover from an incident. I can immediately see why we might focus on prevention, as if a cyber incident doesn’t happen, then things are all good. The reality however is that cyber incidents are almost guaranteed. And if we accept that an incident is definitely going to happen at some point in the future then we are better spending a little less time focussed on prevention and a little more on considering what we will do when an incident does happen. This can easily be done through desktop exercises, and doing so is always preferable to actually having to work it out when the world is on fire in the midst of a real cyber incident. And to that end I actually delivered a little exercise only the other day.
People, Processes and Technology
One of the biggest takeaways from the event was the mention of People, Processes and Technology (PPT for short, and not the Microsoft App). Sadly all to often we focus on Technology. How can we technically keep data secure? How can IT deliver training to those clicking a phishing link? What we need to do more of is to consider the people involved and their impact, as well as the processes. If we consider people, processes and technology we likely will have the best opportunity of keeping things secure and safe. And I note, that considering people, processes and technology isn’t just an infosec thing, it can equally be applied to school technology strategy, to use of technology in classrooms, and much more.
I suspect as we continue to make use of more technology and as technology further pervades every aspect of our lives, we need to increasingly seek to look to the human contribution and to human behaviour, rather than getting so focussed on the tech.