Passwords continue to be a key feature of identity management. As such we need to continue to educate and build awareness around passwords and password management.
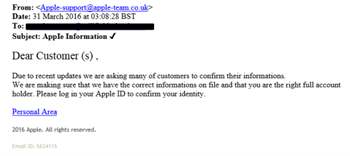
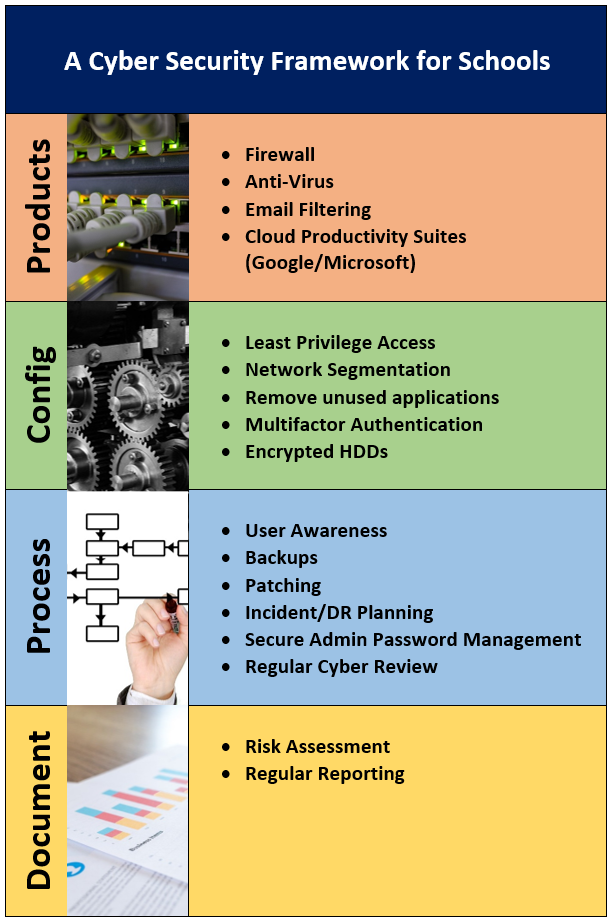
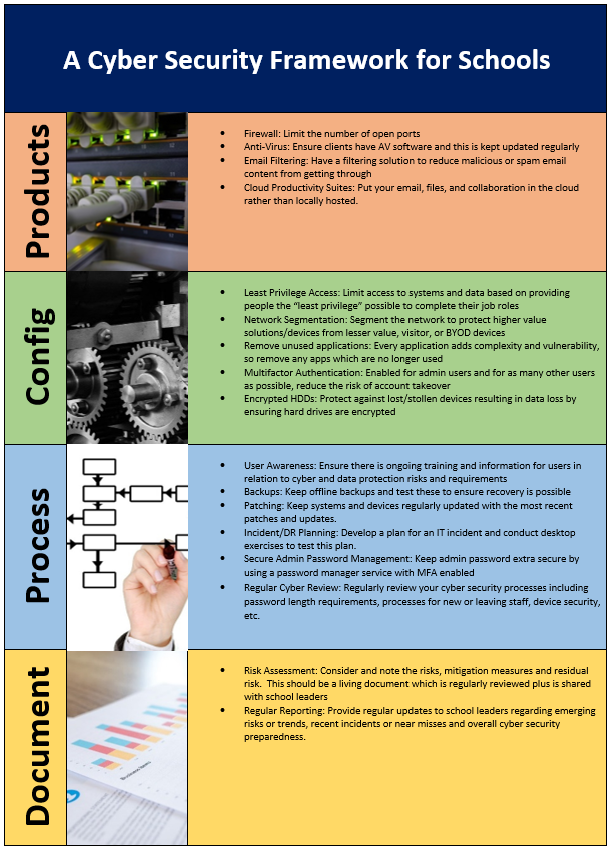
As such I have noted a graphic like the below (taken from Hive Systems via Tech Republic) regularly shared in relation to the time taken to crack a password based on different scenarios of password format and length. The issue for me is that the below paints a picture, which although useful in some ways, overly simplifies the situation.

Statistics, statistics and more statistics
The graphic is based on the time taken to progress through all known combinations for a given password. So, for example, to crack a password of 8 characters based on numbers-only I need to first know that the password is made of numbers-only and therefore that I am only testing these combinations. So, I would test 1 then 2, 3, 4 and just keep going up through the options. Now it might be fair to always test numbers-only first, expecting use of numbers-only to be common enough and therefore low hanging fruit for a cyber criminal’s point of view. It might then equally be fair to suggest that lowercase, mixed case and numbers and mixed case with special characters might each be tested in order based on likelihood and number of combinations presented. At this point the exercise is feeling like an exercise in obsessive compulsive disorder, in going through every possible combination in sequence, rather than an exercise in trying to quickly and efficiently crack a given password.
And to make matters worse if my password happens to be “Password” or “Password22” then I suspect it would be cracked far faster than the reported 2 mins or 3 weeks respectively.
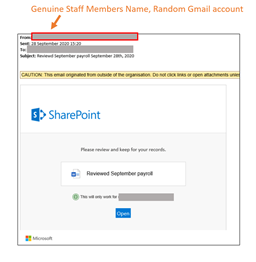
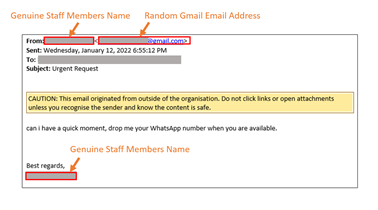
Human behaviours and social engineering
The issue here is, if we are truly trying to be efficient in cracking a password we would approach from a heuristic point of view and look at common human behaviours. We would look at the need for people to remember passwords easily and therefore identify the likely tendency to pick common passwords, passwords relating to recent events or seasonal celebrations, etc. Rather than seeking to work through every combination we would seek to work through the most common combinations and variations of these common combinations, happy in the fact that as a human set the password they may have fallen into one of these common human behaviours. And it is at this point that the graphic no longer works for me.
We would also look towards other data as passwords are not set in isolation. We each set our passwords against the backdrop of our everyday lives, our work, our challenges and our successes, so access to any data on these things can yield information which can be helpful in cracking a password. And oh, does social media and a quick google search help to provide this data. So again, the graphic starts to fail us.
What makes a strong password?
Password length definitely does help in making passwords stronger so in this feature the graphic is useful, but it isnt the single measure which I think the graphic implies it to be. As to the mix of uppercase and special characters, etc, I think in this day and age, this makes limited, but I cant say no, impact on strength.
The factor that the graphic badly misses is the issue of how common the password is likely to be. If it is common, so relating to a current event or a seasonal event, to the company you work for, or to something else that might be predictable based on the world we live in or you as an individual, based on what can be publicly ascertained about you, then the graphic falls flat on its face.
So, what can we do about it?
I think sharing this graphic is useful in terms of pushing the need for longer passwords but I think we should take when sharing this graphic on its own. I think it is useful sharing HaveIBeenPwned’s password testing functionality alongside the graphic such that individuals can use the graphic to assess the length but then use HaveIBeenPwned to assess how common a password is, in the number of times it has appeared in recorded and reported data breaches.
As is often the case, as we seek to find and communicate a message, making it as simple as possible we start to lose some of the detail, and in this case I think the importance of how common or predictable a password is, is a key detail which mustn’t be lost.
References:
Lance.W. (2022) ‘How an 8-character password could be cracked in less than an hour’, TechRepublic, 7th March 2022. Available at: How an 8-character password could be cracked in less than an hour | TechRepublic (Accessed: 12/04/2022).