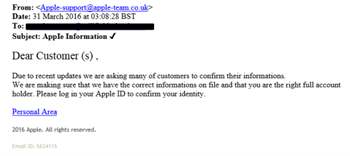
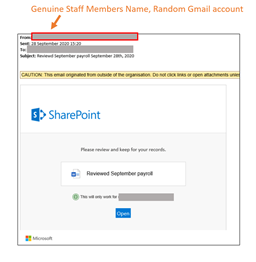
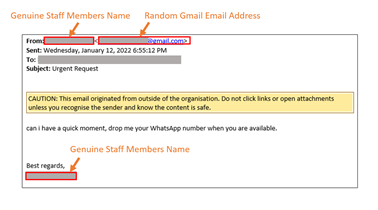
Phishing emails continue to be one of the most common attack vectors used by cyber criminals, in attacking individual and organisations, and in attacking schools colleges and other educational organisations. In schools, where things are increasingly busy, it is important that staff and students have had appropriate training and other resources provided in order to build their awareness and hopefully make them better at identifying such phishing emails. The challenge though is how do we know if our phishing awareness programme is actually working?
I was originally very reluctant to make use of phishing awareness tests, where a fake phishing email is sent out to assess how many staff would fall for a phishing email plus how many staff might report receipt of a phishing email. I felt at the time that it was a little unethical in trying to entrap people who work for my school. I was also worried people would feel it unfair and adding to workload at a time when everyone is already busy. It wasn’t until an IT conference event where I got discussing the issue with someone working within the police force that my view changed. The catalyst for this change being this point; would I rather identify how susceptible the school is to phishing emails and how good individuals are in relation to reporting malicious emails due to a real phishing email, and the likely compromise of user accounts, or would I prefer to gain this information through a safe test where I would be able to respond and do something about the findings.It didnt take me long to realise I was better off testing awareness on my own terms rather than waiting for a cyber criminal.
Since this change of views I have set about regular phishing awareness tests on small groups of users, refining the approach and the follow up messaging and training materials as a result of the findings. Tests might be targeted on certain areas or departments based on recent events or based on trends we are seeing in the types of phishing emails being seen or reported. Follow up training might focus on the users who were tested or might take the data from a test and share it with all staff to highlight specific concerns or areas for improvement. In some cases individuals have felt unfairly treated or “entrapped” however generally have been more understanding when my changed reasoning has been explained to them. The main aim is for the testing and the related awareness development programme to be dynamic in nature, constantly changing in response to the external context and the internal awareness levels and habits as identified from the test data.
Phishing awareness testing doesn’t improve cyber security or users phishing awareness however it can provide a snapshot of where we are at a particular moment of time and in relation to a specific style or type of phishing email. This, when used in combination with dynamic training materials, can be powerful in building up user awareness of phishing emails, of how to identify them and of what to do when things go wrong and you fall for a phish. Where phishing tests are conducted regularly, with the appropriate follow up training, communication and awareness development, it can also go to help develop a culture of cyber security and this, ultimately, is what we really need to achieve.