
It’s been a few days since the JISC Security Conference however I am only now seeing light at the end of the tunnel, having spent the last few days catching up following my two days out at the event. As such I thought I would share some thoughts following Day 2 of the conference.
Defend as one
During the course of the 2nd day of the conference I attended a number of sessions where various educational institutions shared their experiences of cyber incidents. I will admit it was good to hear their experiences as generally all we get to hear of in relation to cyber incidents in schools, colleges, and universities, is the news posts which lack any of the detail as to the cause and impact of the incident, or of the resulting recovery operations. It would be good to hear more of the details around cyber incidents in schools, etc, as there is a great opportunity for use to learn from the experiences and collectively seek to be more secure, with this being summed up by the JISC conference tag line, “Defend as one”. I will however note the challenges in relation to this due to the sometimes sensitive nature of such information.
Cyber: An IT issue?
Now the event itself was very useful for me as a Director of IT, being surrounded by others in similar roles however, as identified by one of the speakers, this also represents a challenge. Technology security is not solely the responsibility of IT. It is the responsibility of all those who use technology, who manage or are the owners of data, who lead departments and who lead or govern within educational institutions. Equally all these people need to be onboard and considering what they might be doing in the event of a critical technology incident where they will need to try to keep operations going while the IT team focusses on the technical issue. Yet the JISC security conference was mainly attended by IT people. Clearly there is need for others to be more engaged, and I will certainly be looking to try and encourage other non-IT senior staff to attend events like this in the future.
Third Parties and supply chain risk
As the second day proceeded, I started to see some key themes and messages coming out, some of which aligned with some of my thinking, with one of these being the risk associated with third parties and the supply chain. Increasingly we are using more external solutions, either online based solutions, or solutions where we have technology solutions from a third party running on our networks. Examples might include a third party hosted web-site solution, a CCTV solution hosted on site, or a visitor management solution hosted on site. These solutions have access to school data or may be on the school network, and as such may either represent a risk to the data should they suffer a cyber incident or could represent a risk to the school network. If on the school network, they might introduce vulnerabilities, which we are unable to address and where instead we must wait for the supplier to identify and resolve by developing and deploying an update or patch. So this risk highlights the need for due diligence before introducing new solutions. This didn’t really happen during the pandemic, as we sought to act quickly to address the challenges so there is work to do in carry out the due diligence for systems now in use. Also, due diligence at the point of purchase represents a snapshot; Most technology solutions evolve over time, with new functionality being added or existing functionality adjusted and changed, meaning the due diligence which was originally conducted is now out of date and inaccurate. This highlights the need for periodic review, but this is then yet another task or piece of work which needs doing, and who does this due diligence where departments across a school, college or university as sourcing their own solutions? For me the key here is we need to look to do more in relation to examining the cyber resiliency and disaster recovery plans of the third parties we use.
Prioritisation
Another theme which came across was the extent of the cyber incidents described. Basically, in some cases it meant going back to scratch, turning everything off and rebuilding. But this takes significant time running into weeks and months. This means it is key to identify the priorities for the recovery. What systems and processes need to be recovered first? If we don’t stop and consider this now, when things are running, we will likely find ourselves in the middle of an incident with every department and users screaming that they system or process is most important, and we will then waste significant time trying to debate and decide. Clearly there is need to examine all the systems and technology in use and then identify a clear and documented priority order for these systems such that when an incident occurs there is a clear priority order with which to work with.
Data Governance
The issue of data governance was particularly notable in discussions related to HE, to universities and this is likely due to their size and scope when compared with schools and colleges. That however is not to say that the same challenges don’t also exist in schools and colleges. The key question here is about the basics of data management and knowing what data we have, why we have it, where it is and likely most importantly who is responsible for it. And in terms of responsibility, I am not referring to IT teams being responsible as they run the systems the data is stored on, but who the owner of the data is. For example, admissions data doesn’t belong to IT, it belongs to the admissions team, while pastoral data belongs to the pastoral team. IT can never know the processes and uses of all the data stored by different depts on IT solutions, therefore they cannot therefore be responsible for the data management side of such data. It is the data owners that are responsible for what data they gather, how it is stored, how long they keep it, etc. It was key from some of the discussions that greater effort needs to be made to ensure all understand who is responsible for what data.
Conclusion
There was a lot to think about on Day 2 and to be honest I havent as yet had a sufficient amount of time to properly stop and reflect on the day or on the wider conference as a whole. And I suspect it will be a few weeks and maybe the end of term before this will properly happen.
That said the above represents some of my initial thoughts based on some of the copious notes I took during the course of day 2.
I will end on an important message as I see it; This can all seem like doom and gloom. The “when” rather than “if” of a cyber incident, the size and impact of such an incident and the multiple things we need to be doing to prevent and prepare, but against the backdrop that no matter what we do it may still happen. We cannot allow it to be all doom and gloom. My view is therefore that we need to simply seek to continually improve, to not try and do everything, but to try and seek to be more secure today than we were yesterday.

 It is important to firstly acknowledge that our views on technology are very much the result of our experiences. My experiences include learning to code in Basic on the Commodore 64 at an early age, before moving on to AMOS basic on the Amiga and then QBasic, Visual Basic and C++ on the PC. This early use of technology, and the ability to develop software to solve problems has very much shaped my views. Now, today I walk around with a mobile phone with over a million times more memory than my commodore 64, from less than 30 years earlier, and the growth rate across the period has not been linear. A perfect illustration of this lies in how long it took various technologies to reach 50 million users. Radio took 75 years whereas TV only took 38 years. Bringing us close to today, Facebook got the time to 50 million users down to 3.5 years before Pokemon go managed it in less than a single month. It is clear from this that the pace of changing is quickening.
It is important to firstly acknowledge that our views on technology are very much the result of our experiences. My experiences include learning to code in Basic on the Commodore 64 at an early age, before moving on to AMOS basic on the Amiga and then QBasic, Visual Basic and C++ on the PC. This early use of technology, and the ability to develop software to solve problems has very much shaped my views. Now, today I walk around with a mobile phone with over a million times more memory than my commodore 64, from less than 30 years earlier, and the growth rate across the period has not been linear. A perfect illustration of this lies in how long it took various technologies to reach 50 million users. Radio took 75 years whereas TV only took 38 years. Bringing us close to today, Facebook got the time to 50 million users down to 3.5 years before Pokemon go managed it in less than a single month. It is clear from this that the pace of changing is quickening. The more I think about the pace of change and the way that technology is becoming an integral part of our everyday lives the more the movie Ready Player One comes to mind. In the movie Wade Watts makes use of virtual reality to live a double life, living as Percival in VR. As the film progresses it becomes clear that his two lives aren’t as separate as he would like and that events in virtual reality impact on real life and vice versa. For us, like Wade Watts, our lives in real life are inseparably linked to our digital lives. In fact, I believe that it no longer serves us to think of digital citizenship as the term implies that there is something else available, a non-digital citizenship, when in fact there is not. Possibly the discussion should not be of digital citizenship at all but simply citizenship. As Danah Boyd, in her book, Its Complicated said, although the apps might change our online connectedness, our need to share and the challenges around privacy are “here to stay”.
The more I think about the pace of change and the way that technology is becoming an integral part of our everyday lives the more the movie Ready Player One comes to mind. In the movie Wade Watts makes use of virtual reality to live a double life, living as Percival in VR. As the film progresses it becomes clear that his two lives aren’t as separate as he would like and that events in virtual reality impact on real life and vice versa. For us, like Wade Watts, our lives in real life are inseparably linked to our digital lives. In fact, I believe that it no longer serves us to think of digital citizenship as the term implies that there is something else available, a non-digital citizenship, when in fact there is not. Possibly the discussion should not be of digital citizenship at all but simply citizenship. As Danah Boyd, in her book, Its Complicated said, although the apps might change our online connectedness, our need to share and the challenges around privacy are “here to stay”.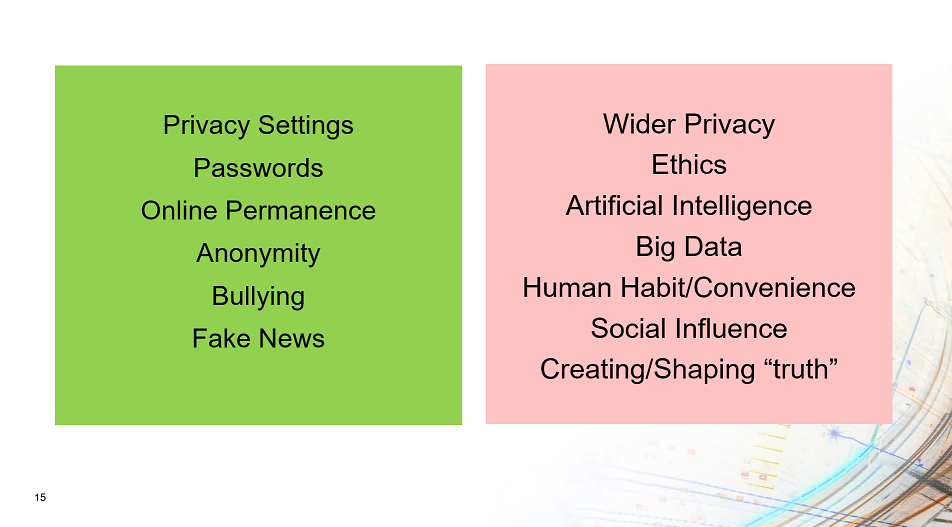 Looking at how we prepare our students for the world and the issues listed above I can see the things which we do satisfactorily, through our eSafety programmers, however I can also see those areas where little or nothing is currently offered. We currently discuss the importance of privacy settings on social media, of having strong passwords, of how online content, once posted, will remain permanent and of the need to be aware of bullying online. These areas are currently covered. Sadly, however little is said in relation to the conflict between user convenience and individual privacy, between individual privacy and public good, and between social media reporting on or actually creating the news and truths which we come to believe. These are the areas which we need to discuss, for which there isn’t a single answer and therefore where the most we can do is help students develop their own views through discussion. It is through discussion that we can hopefully ensure that students, when presented with the infinite challenges of technology use, will approach them with their eyes wide open.
Looking at how we prepare our students for the world and the issues listed above I can see the things which we do satisfactorily, through our eSafety programmers, however I can also see those areas where little or nothing is currently offered. We currently discuss the importance of privacy settings on social media, of having strong passwords, of how online content, once posted, will remain permanent and of the need to be aware of bullying online. These areas are currently covered. Sadly, however little is said in relation to the conflict between user convenience and individual privacy, between individual privacy and public good, and between social media reporting on or actually creating the news and truths which we come to believe. These are the areas which we need to discuss, for which there isn’t a single answer and therefore where the most we can do is help students develop their own views through discussion. It is through discussion that we can hopefully ensure that students, when presented with the infinite challenges of technology use, will approach them with their eyes wide open. I thought I would share some initial thoughts following day one of JISC DigiFest. The event was launched with a very polished and professional pre-prepared video displayed on screens scattered around the events main hall, focussing on the rate of change in relation to technology and some of the technological implications of technology on the world we live in. The launch session also included a room height “virtual” event guide introducing the sessions and pointing you in the direction of the appropriate hall. In terms of the launch of a conference this was the most polished and inspiring launch I have seen albeit on reflection there wasn’t much particularly innovative or technically complex about it.
I thought I would share some initial thoughts following day one of JISC DigiFest. The event was launched with a very polished and professional pre-prepared video displayed on screens scattered around the events main hall, focussing on the rate of change in relation to technology and some of the technological implications of technology on the world we live in. The launch session also included a room height “virtual” event guide introducing the sessions and pointing you in the direction of the appropriate hall. In terms of the launch of a conference this was the most polished and inspiring launch I have seen albeit on reflection there wasn’t much particularly innovative or technically complex about it. The keynote speaker addressed the changing viewpoints of different generations of people focussing particularly on Generation Z, the generation which currently are in our sixth forms, colleges and universities. I took away two key points from the presentation. The first was how each generations views were shaped by their experiences particularly between the ages of 12 and 20 year old. Jonah Stillman used thoughts on space as an example showing how Generation X might have positive views focussing on the successes of the moon landing whereas Millennials may have a more cynical view following the Challenger disaster. Additionally, Jonah mentioned movies as a social influencer and how those in the Harry Potter generation may view cooperation and trying hard, even where unsuccessful, in a positive manner. Those born later than this may draw on another series of films, in the hunger games, resulting in a greater tendency towards competition and the need to succeed in line with the movies storyline of everyone for themselves and failure results in death. The second take away point from the session resulted from the questioning at the end of the session around what some saw as the absoluteness of the boundaries between generations. I think Jonah’s use of the word “tendency” addressed this concern in that the purpose of the labels was for simplicity and to indicate a general trend and tendency rather than to suggest that all people born on certain dates exhibited a certain trait. It increasing concerns me that this argument keeps coming up when surely it is clear that there is a need to use simplistic models to help clarity of explanation and that no model, not matter how complex will ever truly capture the real complexity of the world we live in.
The keynote speaker addressed the changing viewpoints of different generations of people focussing particularly on Generation Z, the generation which currently are in our sixth forms, colleges and universities. I took away two key points from the presentation. The first was how each generations views were shaped by their experiences particularly between the ages of 12 and 20 year old. Jonah Stillman used thoughts on space as an example showing how Generation X might have positive views focussing on the successes of the moon landing whereas Millennials may have a more cynical view following the Challenger disaster. Additionally, Jonah mentioned movies as a social influencer and how those in the Harry Potter generation may view cooperation and trying hard, even where unsuccessful, in a positive manner. Those born later than this may draw on another series of films, in the hunger games, resulting in a greater tendency towards competition and the need to succeed in line with the movies storyline of everyone for themselves and failure results in death. The second take away point from the session resulted from the questioning at the end of the session around what some saw as the absoluteness of the boundaries between generations. I think Jonah’s use of the word “tendency” addressed this concern in that the purpose of the labels was for simplicity and to indicate a general trend and tendency rather than to suggest that all people born on certain dates exhibited a certain trait. It increasing concerns me that this argument keeps coming up when surely it is clear that there is a need to use simplistic models to help clarity of explanation and that no model, not matter how complex will ever truly capture the real complexity of the world we live in.