While at the School and Academies Show one of the discussions I had focussed on general EdTech and the need for teachers to model appropriate digital, including cyber security, behaviours for students. As the discussion progessed it then moved over to the topic of data protection, and I think this hit a chord with me.

Seeking solutions
The pandemic has required us to be agile in quickly finding solutions for issues, ways to engage learners and bring about the best learning experiences where students are either all online, away from the classroom, or where we have a hybrid situation, with some in the class and some not. The issue is that the resulting search for solutions has led to tools, which may have pedagogical benefit being adopted which the due diligence as to data protection.
All staff need to appreciate that where signing up to an online service they are giving away some data. It might seem as simple as an email address and password, but the reality is most services will also look at IP addresses, which gives away some rough geographical information, plus information on the device being used such as the browser, device type and operating system. Then dependent on the nature of the service itself, they will then gather further data as provided by us, but also in relation to when we access a service and how often, and also which others in similar geographical areas, based on IP address, tend to access the service at the same time.
And this is all before, as a teacher, I then get students to sign up for the same service as it is useful in the teaching of my given subject or a specific topic. So now, students are also giving away data but at my request.
Data Protection and GDPR
I think part of the issue here is that all staff are not IT experts or data protection experts. But yet we all sign up to services which in effect gather the data we provide, and some data we don’t quite realise they are gathering. For me the issue here is that, although we may not be experts, we need to exercise some care in relation to data protection. Now this might be simply looking at the privacy policy for anything which seems out of place. It might be seeking support from the IT team in a school, or seeking support of educators the world over via twitter or other forums. The key thing is we cant simply sign up without given some consideration to the risks and implications of doing so.
Now those in the data protection world may see the above as not going far enough, they may state GDPR UK or other legislation however the reality, in my view, is most things boil down to risk based decision making. The role of a school is not to be as secure in its data protection as a bank or other highly regulated industry, but to facilitate learning. So there are some trade offs, where learning takes the priority and some risks are accepted, and hopefully, mitigated as much as is possible.
Conclusion
I think all schools need to spend some time discussing the implications of signing up for online services, and to data sharing with all staff. We can’t hope to make them experts but we can hope to educate them enough to give some reasonable consideration to the implications of their actions in signing up for a service, or where getting students to sign up for an online service. Its about doing all we can to reasonably facilitate good data protection based decision making and behaviours, in both staff and through modelling, in students.


 I have previously written about third party related cyber risk in relation to data protection and GDPR but I think it warrants a little bit of a further discussion. To start I will state what I believe is the key message:
I have previously written about third party related cyber risk in relation to data protection and GDPR but I think it warrants a little bit of a further discussion. To start I will state what I believe is the key message: A German state have announced that they are banning the use of Office 365 in their schools citing GDPR reasons (read article
A German state have announced that they are banning the use of Office 365 in their schools citing GDPR reasons (read article  The recent announcement of the proposed fine of British airways has once again re-ignited the GDPR related discussion. The fact that it was followed promptly by a further fine for the Marriot hotel chain just added fuel to the fire. I have once again seen a number of emails and posts on social media regarding GDPR support and consultation services and also GDPR “solutions”. This continues to worry me as the security and protection of organisational data is an ongoing process and not simply a task to be done and then revisited yearly or a product/service to be purchased. It also worries me that some schools or even other organisations may sign up to services seeking an answer however will find that their purchase adds little value but at significant cost.
The recent announcement of the proposed fine of British airways has once again re-ignited the GDPR related discussion. The fact that it was followed promptly by a further fine for the Marriot hotel chain just added fuel to the fire. I have once again seen a number of emails and posts on social media regarding GDPR support and consultation services and also GDPR “solutions”. This continues to worry me as the security and protection of organisational data is an ongoing process and not simply a task to be done and then revisited yearly or a product/service to be purchased. It also worries me that some schools or even other organisations may sign up to services seeking an answer however will find that their purchase adds little value but at significant cost.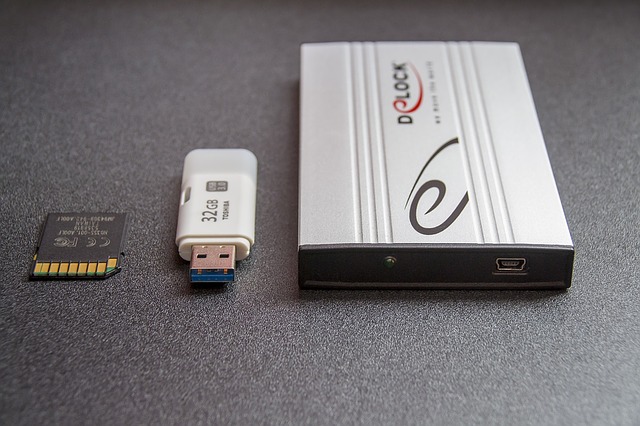 USBs
USBs
 Recently a member of staff popped in to discuss how she would like to share photos of a school sporting event with the various schools which were involved. This got me thinking about GDPR and the implications for events and photography at such events.
Recently a member of staff popped in to discuss how she would like to share photos of a school sporting event with the various schools which were involved. This got me thinking about GDPR and the implications for events and photography at such events.